General
Enterprise TMS Security Compliance: A Strategic Guide for Logistics Leaders
Apr 15, 2026
20 mins read

Key Takeaways
- Enterprise TMS platforms now process real-time GPS feeds, carrier financials, driver PII, and AI dispatch decisions across 15 to 40 active integrations, making the integration layer the primary attack surface for sophisticated threat actors.
- SOC 2 Type II certification covers the TMS vendor’s internal controls and transfers no compliance obligation to the enterprise, regardless of what the vendor’s security questionnaire implies.
- Multi-tenant TMS environments used by 3PLs carry cross-tenant data exposure risk when tenant isolation is enforced at the application layer but not at the database query layer, a gap a single misconfigured API call can exploit.
- AI-powered TMS features, including automated dispatch and dynamic route optimization, introduce model poisoning, adversarial input, and auditability requirements that standard TMS security frameworks do not address.
- Enterprises evaluating 3-5 year vendor partnerships should require TMS vendors to document their post-quantum cryptography roadmap against NIST FIPS 203, 204, and 205, finalized in August 2024.
A single misconfigured API endpoint in a TMS platform can expose shipment data across thousands of enterprise orders, carrier rate agreements worth millions, and real-time location feeds for an entire fleet.
The IBM Cost of a Data Breach Report 2025 puts the average global breach cost at $4.44 million, with supply chain incidents involving third-party integrations consistently exceeding that baseline.
Most enterprise logistics leaders inherited their TMS security posture rather than designed it. The platforms evolved from routing tools into AI-powered orchestration engines processing real-time data across dozens of live integrations, and the attack surface grew with each new carrier connection, telematics feed, and ELD integration.
The TMS vendor’s SOC 2 Type II certificate covers their controls. The configuration inside it is entirely yours.
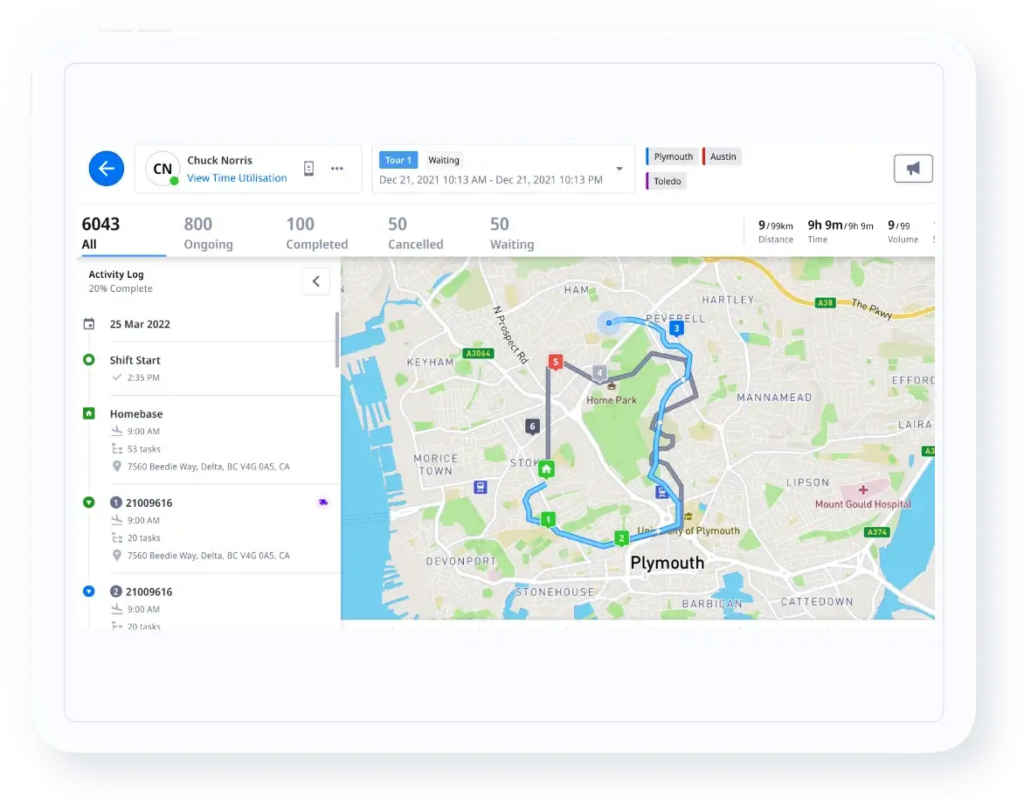
The framework in this guide covers enterprise TMS security compliance across four architectural layers: data protection, access controls, integration security, and governance. It draws on Locus’s experience securing AI-driven logistics orchestration across six global regions and addresses the AI-specific risks, multi-tenant isolation failures, and regulatory developments most vendor documentation treats superficially.
Why Security Compliance Is Now a Board-Level Priority for Enterprise TMS
Enterprise TMS security compliance requires a structured approach across four layers, such as data protection (encryption standards and residency), access controls (RBAC, MFA, ZTNA), integration security (API hardening, carrier credential management, ELD data provenance), and governance (incident response, audit cadence, vendor vetting).
Enterprises with multi-region operations face layered regulatory obligations, including SOC 2 Type II, ISO 27001, GDPR, KSA PDPL, and India’s DPDP Act, each applying to different data types and geographies.
The compliance conversation shifted when TMS platforms moved from batch-process routing tools to continuous, event-driven orchestration engines. A modern enterprise TMS ingests real-time GPS feeds, customer PII, carrier contracts, freight invoices, driver hours-of-service data, and AI dispatch decisions simultaneously, across dozens of live integrations. Sophisticated attackers know this.
Hardened core TMS systems attract comparatively less attention than the 20 to 40 API connections surrounding them, each maintained by vendors with uneven security practices.
The expanding attack surface
In North America, ELD hardware vendors have historically prioritized HOS compliance over data security, meaning ELD-to-TMS data streams frequently run on weakly encrypted channels.
A compromised ELD feed can inject falsified hours-of-service data into the TMS, creating both compliance liability for the carrier and corrupted routing inputs for the dispatch engine. For an enterprise TMS with 30+ carrier integrations, each integration introduces a distinct credential set, a separate trust boundary, and a distinct audit trail requirement.
Locus’s experience operating across North America, the EU, SEA, India, and MEA confirms the security risk in enterprise TMS deployments concentrated at the integration layer. Multi-region scale amplifies the number of integrations faster than most security teams anticipate.
Quantifying the exposure
A 3PL with 30 or more active carrier integrations faces a compounding problem. When carrier API credentials are stored at the application layer rather than in a secrets management vault, a single TMS environment breach simultaneously exposes every carrier relationship. The operational consequence is a shutdown across the full carrier network.
The second risk is structural. The SOC 2 Type II certificate your TMS vendor holds covers their internal controls. It says nothing about how your organization has configured data retention policies, permission hierarchies, or integration security within the deployment itself.
TMS Compliance Requirements by Region: SOC 2, GDPR, PDPL, and Beyond
Enterprise TMS compliance is not a single standard. It is a layered set of obligations determined by where data originates, where it is processed, and what type of data it represents. Shipment records, driver PII, real-time location feeds, and carrier financial data each carry distinct regulatory obligations.
For enterprises operating across multiple geographies, those obligations overlap in ways a single deployment model cannot resolve. Understanding last-mile technology security considerations by data type is the first step in mapping those obligations accurately.
Core certifications and what they actually cover
SOC 2 Type II is the baseline: it confirms the vendor’s security controls operated effectively over a defined audit period. The scope is the vendor’s systems, not the enterprise’s configuration of them.
ISO 27001 is the information security management standard covering risk assessment, access control, and incident management organization-wide. ISO 31000 adds the risk management framework above it.
For regulated data types, HIPAA governs health-adjacent logistics (pharmaceutical cold chain, medical device distribution), and GDPR governs any personal data involving EU-based individuals, including drivers, couriers, and end customers.
Regional mandates and the data residency problem
KSA’s Personal Data Protection Law (PDPL) requires personal data of Saudi residents to be stored within the Kingdom for specified categories. The trap many enterprises discover too late: global TMS vendors frequently offer KSA “compliance” through contractual data processing agreements rather than in-Kingdom data storage.
When a Saudi enterprise receives a data processing agreement instead of an architecture diagram confirming in-Kingdom infrastructure, they face direct NCA audit exposure. The National Cybersecurity Authority flagged this pattern in multiple enterprise deployments from 2023 onward.
India’s DPDP Act (2023) requires consent, purpose limitation, and data localization for specific categories. Southeast Asia is fragmented: Thailand’s PDPA, Malaysia’s PDPA, and Indonesia’s PDP Law carry distinct cross-border transfer restrictions and breach notification timelines incompatible with each other or with GDPR.
What built-in compliance looks like vs. bolt-on
Built-in compliance means the TMS routes data to the correct jurisdiction at the architecture level: EU customer data stays in EU-hosted infrastructure, KSA driver PII routes to in-Kingdom storage, and regulatory reporting pulls from audit trails automatically.
Bolt-on compliance is a contractual overlay on top of a deployment where data routing is global by default. The procurement test: ask for an architecture diagram showing data flows by jurisdiction. A compliance certificate answers a different question.
| Framework | Scope | Key Obligation for TMS | Applies When |
|---|---|---|---|
| SOC 2 Type II | Vendor security controls | Covers vendor’s systems; enterprise configures within | Evaluating any SaaS TMS vendor |
| ISO 27001 | Organization-wide information security | ISMS, risk assessment, access control | Global enterprise deployments |
| GDPR | EU personal data | Consent, residency, breach notification within 72 hrs | Any EU driver or customer data |
| KSA PDPL | Saudi personal data | In-Kingdom storage for specified categories | KSA operations |
| India DPDP Act | Indian personal data | Consent, purpose limitation, localization for select categories | India operations |
| EU AI Act | Automated decision systems | Transparency and auditability for AI-generated decisions | AI-powered TMS features |
For procurement teams managing multi-region vendor selection, the table above points to a pattern worth noting. GDPR’s transfer restrictions and KSA PDPL’s storage requirements can conflict when carrier rate data involves individuals from both regions simultaneously.
A TMS vendor offering a single global deployment model was not architected for this layer of complexity.
Data Security Architecture That Enterprise TMS Demands
Five technical controls separate enterprise-grade TMS security from mid-market platforms with enterprise-adjacent marketing. Each addresses a specific failure mode in a logistics environment.
Locus’s dispatch management engine and real-time tracking flows operate across encrypted pipelines handling millions of routing decisions per day, making these controls a live operational requirement rather than a compliance checkbox.
Encryption standards
Data in transit must run over TLS 1.3. Older protocol versions carry documented vulnerabilities actively exploited in API-heavy environments.
The logistics-specific exposure point is the dispatch-to-driver data stream: route instructions and confirmations transmitted over weakly encrypted channels are interceptable without access to the TMS core. Encrypted real-time communication in logistics prevents interception at this specific point.
Data at rest requires AES-256, covering stored shipment records, carrier contracts, driver PII, and AI model training data.
RBAC and the tenant isolation failure mode
In 2023, a mid-sized UK 3PL discovered a configuration error in their shared TMS dashboard had exposed Shipper A’s carrier rate agreements to Shipper B’s operations team for eleven months.
It was a default permission setting no one had audited. Two shipper contracts terminated, one legal dispute, and a six-figure settlement followed.
The deeper architecture risk: in many multi-tenant TMS deployments, tenant isolation is enforced at the application layer but not at the database query layer. A misconfigured API call returns data across tenant boundaries when the default query scope is not tenant-scoped at the row level. Ask TMS vendors directly whether row-level security is enforced at the database layer. The distinction between application-layer and database-layer isolation carries materially different risk profiles.
API security and carrier credential management
OAuth 2.0 with token-based authentication, rate limiting, and API gateway controls address the standard threat model.
The logistics-specific failure mode is credential storage. When carrier API credentials are held at the application layer rather than in a secrets management vault such as HashiCorp Vault or AWS Secrets Manager, a single TMS environment breach becomes a multi-carrier credential exposure event.
Enterprises evaluating TMS vendors should ask specifically how carrier credentials are stored, rotated, and revoked, and what the response procedure looks like when a single carrier credential is suspected of being compromised. These questions reveal whether the vendor has architectural security or documentation of it.
Penetration testing cadence and update management
Enterprise benchmark is quarterly penetration testing, with scope covering the integration layer in addition to the core TMS system.
Annual pen tests miss attack surfaces introduced by new carrier connections and telematics onboarding. The harder governance problem is update deferral: TMS patches require carrier integration re-testing, WMS interface validation, and change management sign-off. A patch taking six weeks to clear internal validation leaves the enterprise running a
known-vulnerability version for six weeks. TMS architectures requiring full regression testing for every patch create security debt accumulating with every deferral. Modular, backward-compatible architecture resolves this, and it is a legitimate differentiator to probe during vendor evaluation. The TMS security protocols that prevent operational failure extend well beyond that boundary.
| Security Control | Standard/Protocol | Why It Matters in Logistics | Enterprise Benchmark |
|---|---|---|---|
| Data in transit | TLS 1.3 | Protects dispatch-to-driver and TMS-to-carrier data streams from interception | TLS 1.3 minimum; no legacy protocol fallback |
| Data at rest | AES-256 | Covers stored carrier contracts, driver PII, and AI model training data | AES-256 across all persistent data stores |
| Access control | RBAC with row-level DB security | Prevents cross-shipper data exposure in multi-tenant environments | Granular permission hierarchy; role audits quarterly |
| API authentication | OAuth 2.0 with token rotation | Limits blast radius of a single compromised carrier credential | Secrets vault storage; no application-layer credentials |
| Penetration testing | OWASP with integration layer in scope | Catches new attack surfaces from carrier and telematics onboarding | Quarterly; integration surface included each cycle |
| MFA enforcement | TOTP or hardware key | Blocks credential-stuffing attacks on dispatcher and planner accounts | Mandatory for all admin and operations roles |
The pattern in this table points to one consistent conclusion. The technical control is not the differentiator. The differentiator is whether it is implemented at the architecture level across the full integration surface or deployed as a layer on top of a fundamentally open data model.
Securing AI-Driven Logistics: The Overlooked Compliance Frontier
Automated dispatch, dynamic route optimization, and predictive ETA models each consume real-time data from external sources, and each data source is simultaneously a capability input and a potential attack vector. No currently ranking competitor content adequately addresses this.
Locus’s AI-powered dispatch management and route optimization engine processes decisions across encrypted TLS 1.3 pipelines, with every algorithmic routing decision logged against the input variables at decision time.
Model poisoning and GPS data provenance
A route optimization model trained on historical traffic data can be manipulated by feeding it falsified GPS coordinates from a compromised telematics provider. The algorithm then routes vehicles through systematically longer paths, inflating fuel costs and delivery times across an entire fleet before the deviation appears in operational metrics.
GPS spoofing attacks against navigation systems are documented, with incidents affecting commercial aviation near Ben Gurion Airport having direct analogues in high-value road logistics corridors. The prevention mechanism is data provenance validation at the model input layer: verify the integrity and source of each external feed before it enters the optimization pipeline.
For AI-driven route optimization, the compliance dependency starts at the data input layer, before output processing begins.
Auditability requirements for AI-generated decisions
When an AI-powered TMS assigns a specific driver to a specific route, or holds a delivery for a predicted demand window, the decision must be auditable. Regulators, shippers, and, in some jurisdictions, drivers have standing to ask why the system made a particular assignment.
Without decision logging capturing the input variables, the model version, and the active constraint set at the time of each decision, the enterprise cannot answer that question.
Locus logs every route optimization decision against carrier constraints, traffic conditions, and driver availability inputs, creating audit trails satisfying both SOC 2 Type II controls and the EU AI Act’s transparency obligations for automated decision systems.
EU AI Act and the transparency obligation
The EU AI Act classifies logistics AI as “limited risk” under Article 13, requiring transparency and human oversight. For TMS vendors operating in the EU, decision logs must exist, be accessible, and be structured to answer regulatory inquiries.
AI features added as bolt-ons typically lack this logging infrastructure because the AI layer was added to a system not built with decision-level auditability in its data model.
Locus secures AI-driven dispatch and route optimization for enterprises across six regions. Schedule a demo with Locus to see how its decision logging and encrypted data pipelines map to your compliance framework.
Multi-Tenant Security and Zero-Trust for 3PL and Shared Visibility
3PLs serving multiple shippers, and enterprises sharing visibility dashboards with carriers and fulfillment partners, face a risk category that standard TMS security documentation addresses superficially. The lateral movement risk in multi-tenant environments is real, but the mechanism is what makes it actionable.
Locus’s supply chain visibility platform delivers real-time multi-stakeholder access without compromising tenant-level data isolation, and the architectural reason is worth examining for any enterprise evaluating multi-tenant TMS deployments.
Where tenant isolation breaks down
The failure mode is frequently not a sophisticated attack. In many multi-tenant TMS deployments, isolation is enforced at the application layer. If the database query logic is not tenant-scoped at the row level, a misconfigured API call returns records across tenant boundaries.
A 3PL whose TMS vendor has not implemented row-level security at the database layer is one configuration error away from a cross-tenant exposure affecting every shipper simultaneously. Asking whether tenant isolation is enforced at the application layer or the database query layer is one of the most diagnostic evaluation questions a 3PL security team can ask.
Automated tracking and compliance monitoring across multi-shipper environments depends on the monitoring layer receiving correctly tagged data from the source.
Zero-trust network architecture in TMS
ZTNA applied to TMS means every API call, every dashboard request, and every data export is authenticated and authorized independently, regardless of whether the user is on a trusted network or already authenticated in the session. Carriers granted access to shipment tracking dashboards should see their own freight data, where verification must happen at the data-fetch level rather than at login alone.
Standard implementations authenticate at the session boundary and verify nothing afterward. For a 3PL giving visibility access to 20 carriers simultaneously, this is the difference between controlled access and a permission model correct on paper and porous in practice.
Vendor vetting protocols and SIEM integration
Every telematics provider, ELD system, and WMS integrated with the TMS extends the trust boundary. Vendor security questionnaires address this in principle. The operational test is whether the TMS vendor conducts integration-layer security reviews, maintains a verified integration catalog with documented security postures, and has a defined response procedure when an integrated provider’s credentials are compromised.
SIEM integration closes the gap between configuration-time security and runtime security: the system detects unusual API call volumes, off-hours data exports, and atypical query patterns in real time rather than during a post-breach forensics review.
Building an Enterprise TMS Security Governance Framework
Technical controls create the floor. Governance determines whether the floor holds under operational conditions. The clearest gap in most enterprise security frameworks: TMS incidents are operational crises first and IT incidents second. Building resilient logistics teams means training operations staff to respond to security events as live operational decisions, routing them through command authority rather than through a ticketing system.
TMS-specific security policy
A general IT security policy adapted for TMS use is not a TMS security policy. The distinctions that matter: data retention windows for shipment records differ from those for driver PII. Carrier contract data carries commercial confidentiality requirements separate from regulatory ones. The access control hierarchy for a TMS spans dispatchers, planners, carrier account managers, and field drivers across potentially dozens of geographies. A TMS-specific security policy names each data category, the applicable regulation, the retention window, the permission level, and the audit cadence. A general IT policy names none of these.
Incident response for logistics scenarios
Most enterprise TMS incident response playbooks derive from generic IT security templates classifying a GPS feed disruption as a data integrity event. When 40 vehicles are actively being routed and the GPS feed is compromised, the incident is not an IT ticket.
A dispatch supervisor is making manual routing decisions for a live fleet, potentially for hours, with no algorithmic support. The incident response playbook must define who triggers manual dispatch protocols, what override authority the dispatch team holds during a confirmed spoofing event, and how the decision audit trail is preserved when the AI system is offline. GPS spoofing governance is an operations problem written as an IT problem, and that gap costs operational continuity at the worst possible time.
Remote access policies and update cadence
SSO with ZTNA enforcement for all remote access, including mobile dispatch applications used by field operatives, is the baseline configuration.
BYOD restrictions for driver-facing applications require a separate policy: personal devices accessing dispatch instructions carry different endpoint security profiles than corporate-managed hardware. Software update mandates need a practical governance answer to the deferred-patch problem.
When an update requires six weeks of integration re-testing to clear internal validation, the enterprise needs a documented policy for operating in a known-vulnerability state, including the compensating controls covering the exposure window.
Future-Proofing TMS Security: Quantum Threats, ESG Data, and 2026 Regulations
The planning horizon for enterprise TMS vendor partnerships runs three to five years. Three regulatory and technological developments in this planning window will materially affect security architecture requirements for logistics operators.
Post-quantum cryptography readiness
NIST finalized three post-quantum cryptography standards in August 2024: FIPS 203 (ML-KEM), FIPS 204 (ML-DSA), and FIPS 205 (SLH-DSA). Enterprises should ask TMS vendors today for their migration roadmap from RSA and ECC-based encryption to post-quantum algorithms.
The urgency comes from “harvest now, decrypt later” attack patterns: adversaries capture encrypted TMS data today and decrypt it as quantum computing matures.
ESG data and the compliance intersection
Green routing optimization data, per-delivery emissions tracking, and carbon audit trails are now part of enterprise ESG disclosure requirements under the EU’s Corporate Sustainability Reporting Directive (CSRD). This data sits inside the TMS, and it carries the same access control, audit trail, and integrity requirements as financial data.
Compliant supply chain network design now requires data governance controls alongside operational ones. Manipulated, erroneous, or missing ESG audit trail data creates regulatory liability and reputational exposure increasingly material for enterprises with public disclosure obligations.
NIS2, US critical infrastructure orders, and what enterprises must act on
The EU NIS2 Directive transposition deadline passed in October 2024, and member states are in active enforcement implementation. Logistics operators designated as “essential entities” face mandatory incident reporting within 24 hours, supply chain risk management obligations, and direct enforcement from national regulators.
Enterprises planning multi-year TMS contracts should verify whether their vendor’s incident notification commitments meet NIS2 timelines contractually. US executive orders covering critical infrastructure supply chain security also apply, with logistics classified as a covered sector.
| Threat/Regulation | Timeline | Current Status | Action for TMS Buyers |
|---|---|---|---|
| NIST Post-Quantum Standards (FIPS 203, 204, 205) | Migration window: 2025-2030 | Finalized August 2024 | Request vendor post-quantum migration roadmap today |
| EU NIS2 Directive | Transposition: October 2024 | Member-state implementation ongoing | Verify incident notification SLA is contractually defined |
| EU AI Act (logistics AI transparency) | Phased enforcement: 2025-2027 | Adopted March 2024 | Require decision log documentation for all AI-driven features |
| CSRD ESG data obligations | First reports: FY2024 for large EU enterprises | Active for large companies | Confirm TMS ESG data audit trail integrity controls exist |
| Post-quantum “harvest now” attacks | Ongoing | Current encrypted data at risk | Prioritize quantum-resistant encryption for long-shelf-life commercial data |
TMS vendors reactive to regulatory change require emergency architectural updates when new obligations take effect, typically accompanied by service disruption and contract renegotiation at the worst possible moment.
Vendors with standards-following, adaptable security architectures absorb these changes without forcing enterprise customers back to the negotiating table.
Build Your TMS Security Posture Before the Next Integration Goes Live
Security debt in enterprise TMS accumulates at the integration layer, one carrier connection at a time. The four-layer TMS Security Architecture Stack structures evaluation across Data Layer (encryption, residency), Access Layer (RBAC, MFA, ZTNA), Integration Layer (API security, carrier credential management, ELD provenance), and Governance Layer (incident response, audit cadence, vendor vetting).
Locus is a cloud/SaaS agentic enterprise TMS deployed across six global regions, with SOC 2/ISO-aligned controls, GDPR compliance, RBAC, SSO/SAML, audit logging, and VPC/private cloud options. Pricing is quote-based. It also integrates via RESTful APIs with ERP, OMS, WMS, carrier systems, and telematics.
To evaluate how Locus’s security architecture maps to your compliance requirements, schedule a demo with Locus.
Frequently Asked Questions (FAQs)
1. What security certifications should an enterprise TMS hold at minimum?
At minimum: SOC 2 Type II (not SOC 2 without the Type II designation), ISO 27001, and GDPR compliance if EU personal data is processed. SOC 2 Type II covers the vendor’s controls over a defined audit period. Enterprises with KSA or India operations should require PDPL and DPDP Act compliance verified by architecture diagrams rather than data processing agreements.
2. How does AI-powered route optimization introduce new compliance risks compared to traditional TMS?
AI-powered routing introduces two risks traditional TMS does not face: model poisoning through corrupted GPS or telematics feeds, and auditability gaps in automated decisions. The EU AI Act’s Article 13 requires AI dispatch decisions to be logged against their input variables. Traditional TMS makes deterministic rule-based decisions. AI-generated decisions require dedicated logging infrastructure built for decision-level traceability.
3. What is zero-trust architecture in the context of multi-tenant TMS for 3PLs?
ZTNA in multi-tenant TMS means every API call, dashboard request, and data export is independently authenticated and authorized, regardless of session status. Each shipper’s data must be isolated at the database query layer. Row-level database security prevents a misconfigured API query from returning cross-tenant data even when application-layer access controls are correctly configured.
4. How should enterprises evaluate a TMS vendor’s data residency capabilities for multi-region operations?
Request an architecture diagram showing where each data category is stored, processed, and replicated by jurisdiction. For KSA: verify whether in-Kingdom storage exists as infrastructure or only as a contractual term. For India and Southeast Asia: confirm which specific data categories trigger localization obligations under DPDP and local PDPAs, and how the vendor’s architecture handles each one technically rather than contractually.
5. What steps can logistics leaders take today to prepare their TMS for quantum computing threats?
Request your TMS vendor’s post-quantum cryptography migration roadmap against NIST FIPS 203, 204, and 205, finalized August 2024. Prioritize migrating carrier rate agreements and multi-year contracts to quantum-resistant encryption first. Implement key rotation policies, reducing the exposure window for current RSA and ECC-encrypted data. “Harvest now, decrypt later” attacks mean data encrypted today may be decryptable within the decade.
Written by the Locus Solutions Team—logistics technology experts helping enterprise fleets scale with confidence and precision.
Related Tags:

General
Warehouse Transport System Integration for Enterprise Logistics
How enterprises move from WMS-TMS data sharing to AI-orchestrated dispatch. Covers the maturity model, four ROI metrics, and where leading operations are now.
Read more
General
Role of Procurement Data in Carrier Rate Negotiation: A 2026 Guide
Most enterprise carrier contracts underperform because accessorials, shortfall penalties, and fuel escalation go unmodeled. A framework for procurement teams.
Read moreInsights Worth Your Time

















Enterprise TMS Security Compliance: A Strategic Guide for Logistics Leaders